Current Location: Blog >
Japanese Server
1.
overall architecture overview and design goals
goal: establish a stable, low-latency, and ddos-protected home + cloud hybrid network in japanese native residences (such as ntt optical, au optical, etc.).principle: primary optical fiber + backup mobile/secondary optical fiber + cloud anycast cdn and vps multi-point redundancy.
components: home router (supports vlan/dual wan), local server (nas/home server), tokyo/osaka vps node, cdn/firewall service.
security: use wireguard as site-to-site vpn, and use cloudflare or self-built waf for application layer protection.
scalability: use bgp anycast (provided by the cloud) or keepalived vrrp for local dual-wan switching to support future ipv6 native access.
2.
home line integration strategy and routing solution
main line recommendation: ntt flet's optical (1 gbps symmetrical) as the main egress, with public network static ip or through /29 segment application.recommended line backup: softbank/au 5g router for as backup or second fiber (100 mbps) for load balancing.
router configuration: dual wan ports are configured with policy routing. important outbound traffic is taken through the main line, and automatically switches to the backup line when an exception occurs.
local nat and port mapping: use reverse proxy (nginx) + intranet static ip for key services; avoid directly exposing multiple ports.
qos/bandwidth allocation: prioritize video conferencing and remote working, and limit home entertainment and p2p speed to ensure uplink availability.
3.
vps/host and domain name, dns design
vps roles: reverse proxy/load balancing (tokyo node), backup/synchronization (osaka node), log/monitoring node.domain name design: main domain example.jp, using multiple a/aaaa records to point to vps anycast or different nodes, ttl=300 for fast switching.
dns service: cloudflare dns (with ddos protection) is used as the primary service, and the provider dns (route53 or domestic and foreign second dns) is used as secondary backup.
certificate: automatically issued using let's encrypt, and acme dns verification is used to keep the certificate consistent across multiple nodes.
reverse proxy: nginx or caddy does tls termination and http/2, http/3 support, and internal communication is encrypted by wireguard.
4.
cdn and ddos defense practice
recommendation: place external services on the cloudflare or fastly front-end, and enable waf, rate limiting, and bot management.ddos protection: application layer restriction + network layer anycast cleaning; commercial cleaning (such as akamai/cloudflare spectrum) is effective against udp/tcp attacks.
local traffic management: use the home router to limit the speed of abnormal connections and block suspicious ip segments, and use nftables as rate limiting rules.
logs and alarms: deploy prometheus+grafana on the vps to monitor bandwidth/number of connections, and thresholds trigger sms/email alarms.
recovery process: when traffic is abnormal, it automatically switches to the emergency route that only allows the management interface, and notifies the cloud cleaning service to intervene.
5.
real case: tokyo home + small studio hybrid deployment
background: the customer is located in the 23rd ward of tokyo. it mainly does live broadcasts and remote teaching. it needs low latency and can handle sudden traffic.home line: ntt optical (1 gbps, symmetric, static ip), backup softbank 5g router (300 mbps downlink, backup).
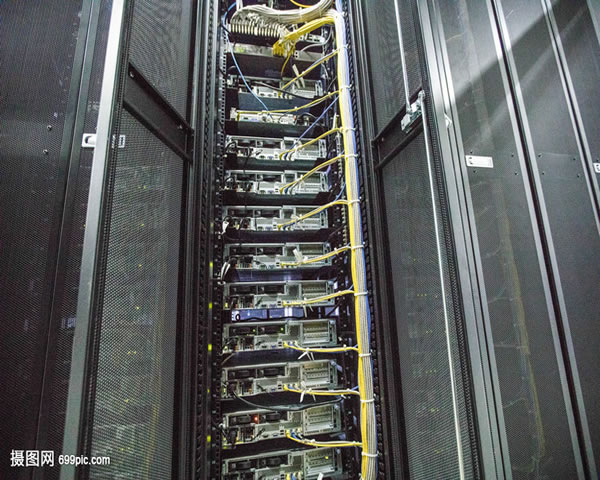
local device: mesh routing + udm-pro/opnsense, vlan division (office/media/guest); wireguard client to connect to vps.
cloud deployment: two tokyo and osaka vpss are used for reverse proxy and media forwarding, with cloudflare cdn in front for caching and ddos protection.
effect: the average rtt is reduced to 20-40ms, the burst access peak is absorbed by cloudflare from the original 500 mbps, and the home uplink availability is stabilized at 80%.
6.
server configuration examples and cost estimates (sample form)
the following table lists typical vps/local nas configurations and bandwidth items for reference:| node | cpu | memory | storage | public network bandwidth |
|---|---|---|---|---|
| tokyo vps (anti-generation) | 4 vcpus | 8gb | 160gb nvme | 1 gbps (shared) |
| osaka vps (backup) | 2 vcpus | 4gb | 80gb ssd | 500 mbps (shared) |
| home nas | 4 corearm/intel | 8gb | 2x4tb raid1 | local uplink 200 mbps |
configuration example: using ubuntu 22.04, wireguard 1.0, nginx 1.22, fail2ban, prometheus monitoring.
backup strategy: vps is rsynced to home nas every day, and key configurations are managed using git and automated deployment (ansible).

- Latest articles
- Where Is The Korean Server Of Warcraft Asia To Teach You How To Quickly Locate The Optimal Node And Delay Optimization Methods?
- Malaysian Server Board Model Differences And Adaptation Suggested Buying Guide
- Practical Cloud Desktop Migration Cloud Computer Malaysia Server Data Protection And Identity Authentication Guide
- Vietnam’s Native Ip Vps Bandwidth Optimization And Cost Control Strategies Are Practical Methods To Improve Roi
- Evaluation Tools And Scripts Are Recommended For The Automated Process Of Singapore Vps Evaluation
- Practical Experience Vps Aws Real Comparison Of Latency And Throughput Between Hong Kong And Other Cloud Vendors
- Alibaba Cloud Japan Cn2 Faq Troubleshooting And Log Analysis Quick Start
- Can I Use Vps From Other Countries To Do Malaysian Tk? A Compilation Of Common Problems And Solutions
- How To Use Starry Korean Vps To Build A Stable Overseas Testing Environment And Backup Strategy
- How Students And Entrepreneurial Teams Can Find A Suitable Solution Within The Budget.
- Popular tags
Nginx
Hybrid Cloud Architecture
Beginner's Guide
Us Ip
Applicable Scenarios
CN2 Optimization
Cross-border Access Speed
Perfect International
US CN2 Server
Guide
Native IP Of The United States
Server Recommendations
America's Fastest Vps
Performance
Common Track Line
Memory
Network Performance
Guide To Using VPS
User Expectations
Display Efficiency
User Impact
Vps Applications
Data Capture
Ddos Defense
American Computer Room
Overseas Distribution Of Corporate Videos
Google VPS
Application Scenarios
Japanese And Korean Markets
Cloudact
Related Articles
-
Guide To Obtaining Japanese Proxy Server Ip Address And Port Number
this article details how to obtain the ip address and port number of a japanese proxy server, including practical steps and how-to guides. -
Why Choose Japanese Native Ip Instead Of Ip From Other Countries?
this article explores why japan’s native ip is chosen instead of ip from other countries, and analyzes its advantages and applicable scenarios. -
Characteristics Of Japanese Native Home Ip And Its Usage Scenarios
discuss the characteristics and usage scenarios of japan’s native family ip, and gain an in-depth understanding of this unique cultural phenomenon.